Account Lockout Event Id Windows 2008 Domain Controller
Simply start the application under an account with the necessary privileges to query the Domain Controllers and do a search for the Event ID 4740 which is the ID for account lockouts on Server 2008 2008R2. This monitor returns the number of changes to the normal logon name or the pre-Win2k logon name.
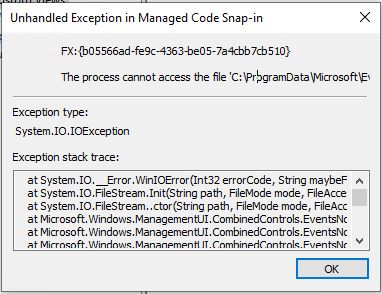 Event Viewer May Close Or You May Receive An Error When Using Custom Views
Event Viewer May Close Or You May Receive An Error When Using Custom Views
The domain account lockout events can be found in the Security log on the domain controller Event Viewer - Windows Logs.
Account lockout event id windows 2008 domain controller. Event ID 4740 - Event properties. This template is assigned to the Domain Controller itself and will return the number of locked out users disabled users etcFor the specific details of which accounts are locked out and when you will find that information in the User Account. Gathers specific events from event logs of several different machines to one central location.
See event ID 4767 for account unlocked. The indicated user account was locked out after repeated logon failures due to a bad password. Note For recommendations see Security Monitoring Recommendations for this event.
Account was locked out Windows Event Log Monitor component details view. LockoutStatusexe uses the NLParseexe tool to parse Netlogon logs for specific Netlogon return status codes. To search the event logs for account lockouts - Start EventCombMT -Right Click on Select to search field Choose Get DCs in Domain Mark your Domain Controllers for search After that on the Searches menu point to Built In Searches and then click Account Lockouts.
For Windows Server 2008 and above replace Event ID field values with 4740. What is consistent is the event number that gets logged when the account is locked out. Heres a screenshot of that event.
With the 4740 event the source of the failed logon attempt is documented. You will see a list of events of locking domain user accounts on this DC with an event message A user account was locked outFind the last entry in the log containing the name of the desired user in the Account Name value. The DC with the PDC emulator role will record every account lockout with an event ID of 4740.
You should see a list of the latest account lockout events. Computer ConfigurationWindows SettingsSecurity SettingsLocal PoliciesAudit PolicyAudit account management Make it a GPO for all Domain Controllers. If you have a single domain controller shame on you then you can skip to the next stephopefully you have at least two DCs.
For more information please refer to the following link. You need to navigate to Event Viewer - Windows Logs - Security and filter current log using Event ID 4740 for Windows 20162012 and Windows 2008 Server or 529 on Windows 2003 Server containing target user name. Determines all the domain controllers that are involved in a lockout of a user in order to assist in gathering the logs.
This is extremely useful when troubleshooting because we can go directly to the domain controller filter for EventID 4740 and it will be able to give us some indication as to whats locking out the account. Enter event ID 4740 in the event ID field. Under the OU for Domain Controllers create a new GPO.
Allows the built-in administrator account to be locked out from network logons. I called mine User Lockout Event Logging so I knew exactly what it was. This event generates every time a user account is locked out.
Forces the client to use a protocol that does not allow the domain controller to get the plaintext password. This event is logged both for local SAM accounts and domain accounts. For user accounts this event generates on domain controllers member servers and workstations.
In an environment with domain controllers running Windows Server 2008 or later when an account is locked out a 4740 event is logged in the Security log on the PDC of your domain. In Windows Server 2008 2012 R2 and 2016 every account lockout gets recorded with the EventID 4740. To find the DC that has the PDCEmulator role run this PowerShell command get-addomain select PDCEmulator.
Free Security Log Resources by Randy. The steps are the same as above I just want to see that the original lockout domain controller can be different and the process or service can be different on the source computer. In this guide were going to focus on event ID 4740.
Account was locked out on DC1 this time at 72725 AM. In the case of the Windows Server 2008-2012 Domain Controller Security. Event ID 4740 is generated on domain controllers Windows servers and workstations every time an account gets locked out.
When an account name is changed the SID remains. Filter the security log by the event with Event ID 4740. Event ID 4767 is generated every time an account is unlocked.
A user account has locked out because the number of sequential failed logon attempts is greater than the account lockout limit. The name of the computer from which the lock was made is specified in the Caller Computer Name value. Account name was changed.
This will quickly filter the event logs and present you with a text file with the results. Filter the security log by the EventID 4740.
 Event Viewer Event Id 4624 See Who And When Logged Into My Computer Youtube
Event Viewer Event Id 4624 See Who And When Logged Into My Computer Youtube
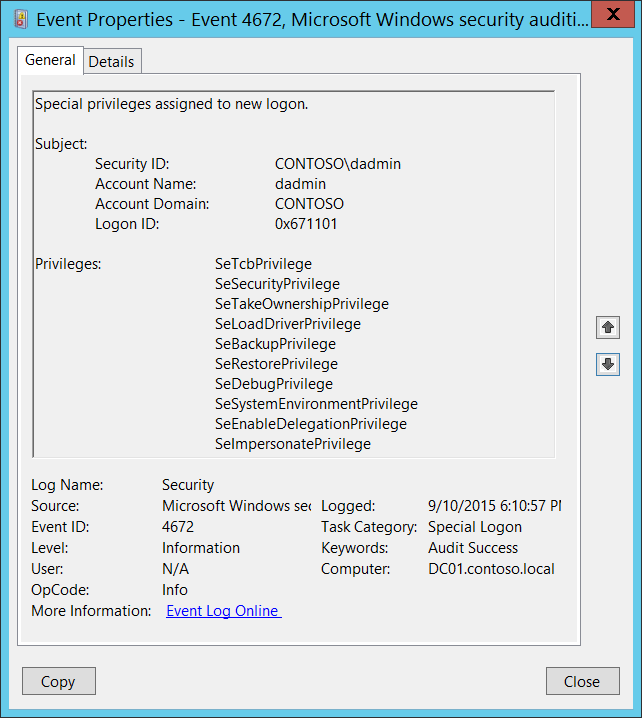 4672 S Special Privileges Assigned To New Logon Windows 10 Windows Security Microsoft Docs
4672 S Special Privileges Assigned To New Logon Windows 10 Windows Security Microsoft Docs
 Fix How To Diagnose Active Directory Account Lockout
Fix How To Diagnose Active Directory Account Lockout
Enabling Event Log Id 4740 A User Account Was Locked Out Danblee Com
 How To Track Password Changes And Resets In Active Directory
How To Track Password Changes And Resets In Active Directory
 Event Id 2087 Dns Lookup Failure Caused Replication To Fail Active Directory Event Id Active Directory Fails
Event Id 2087 Dns Lookup Failure Caused Replication To Fail Active Directory Event Id Active Directory Fails
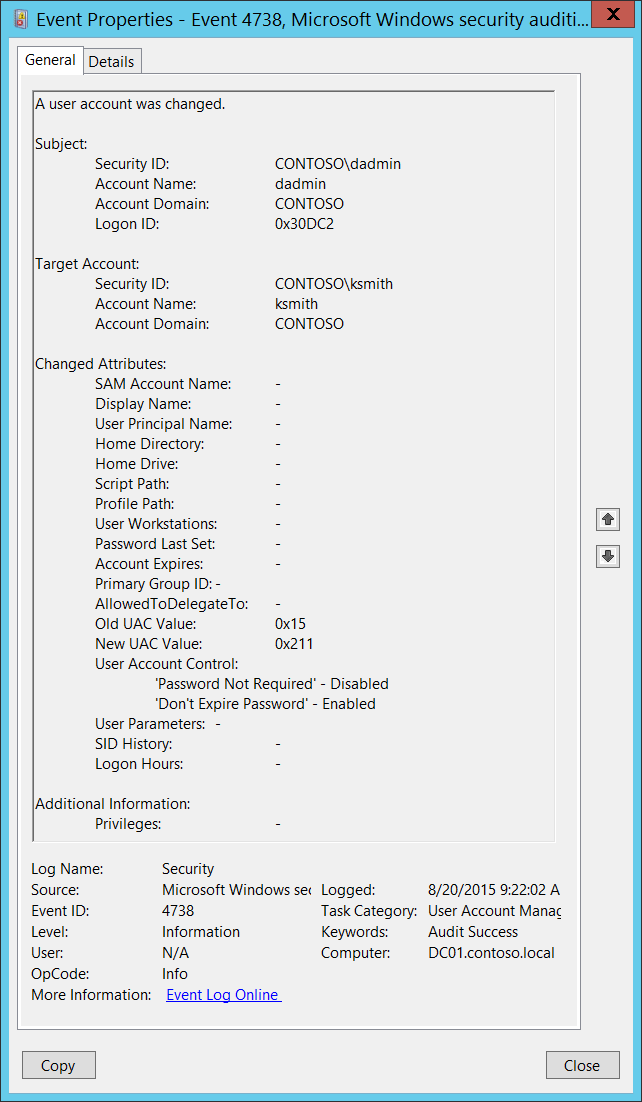
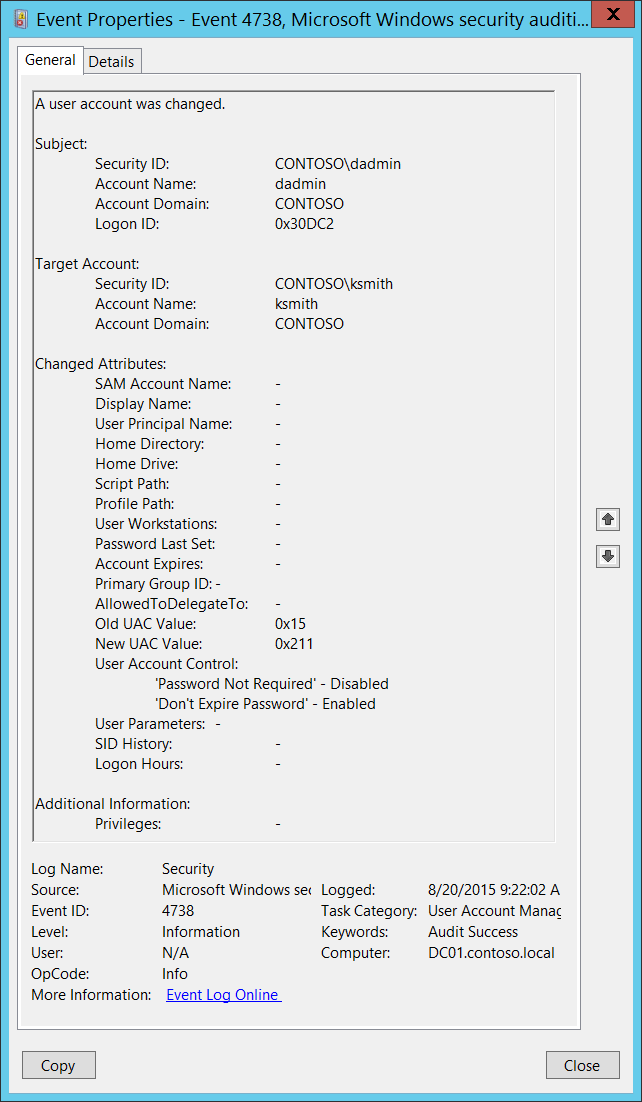 4738 S A User Account Was Changed Windows 10 Windows Security Microsoft Docs
4738 S A User Account Was Changed Windows 10 Windows Security Microsoft Docs
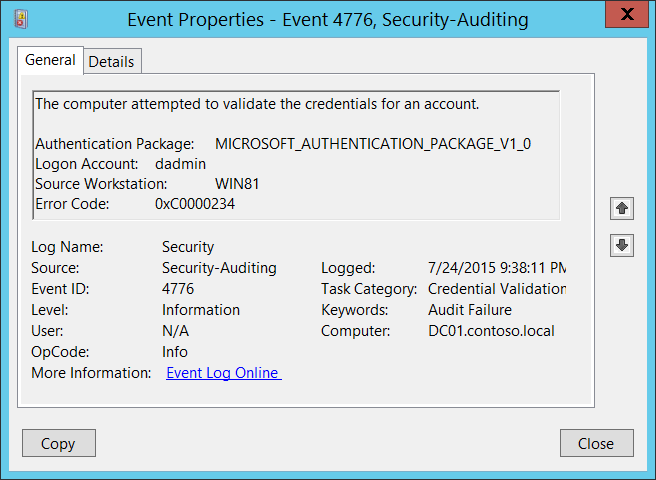 4776 S F The Computer Attempted To Validate The Credentials For An Account Windows 10 Windows Security Microsoft Docs
4776 S F The Computer Attempted To Validate The Credentials For An Account Windows 10 Windows Security Microsoft Docs
 4769 S F A Kerberos Service Ticket Was Requested Windows 10 Windows Security Microsoft Docs
4769 S F A Kerberos Service Ticket Was Requested Windows 10 Windows Security Microsoft Docs
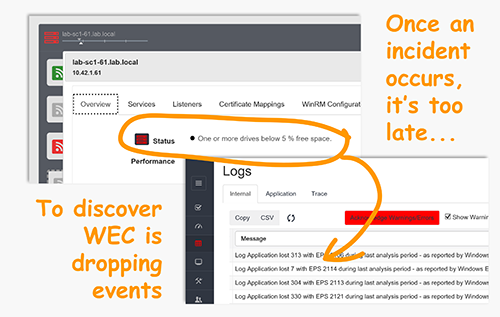
 Ad Fs Troubleshooting Auditing Events And Logging Microsoft Docs
Ad Fs Troubleshooting Auditing Events And Logging Microsoft Docs
 Identify The Source Of Account Lockouts In Active Directory
Identify The Source Of Account Lockouts In Active Directory
Account Lockout On Windows 2008 R2 And Windows 7
 4648 S A Logon Was Attempted Using Explicit Credentials Windows 10 Windows Security Microsoft Docs
4648 S A Logon Was Attempted Using Explicit Credentials Windows 10 Windows Security Microsoft Docs
 Event Viewer Event Id 4740 Account Locked Youtube
Event Viewer Event Id 4740 Account Locked Youtube
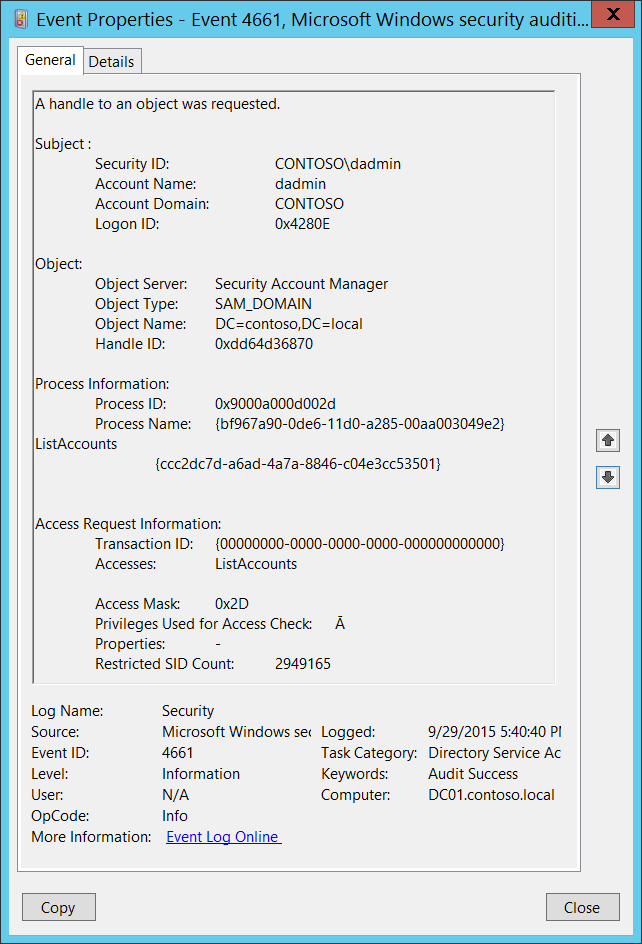 4661 S F A Handle To An Object Was Requested Windows 10 Windows Security Microsoft Docs
4661 S F A Handle To An Object Was Requested Windows 10 Windows Security Microsoft Docs
Windows Event Triggers Windows Os Hub
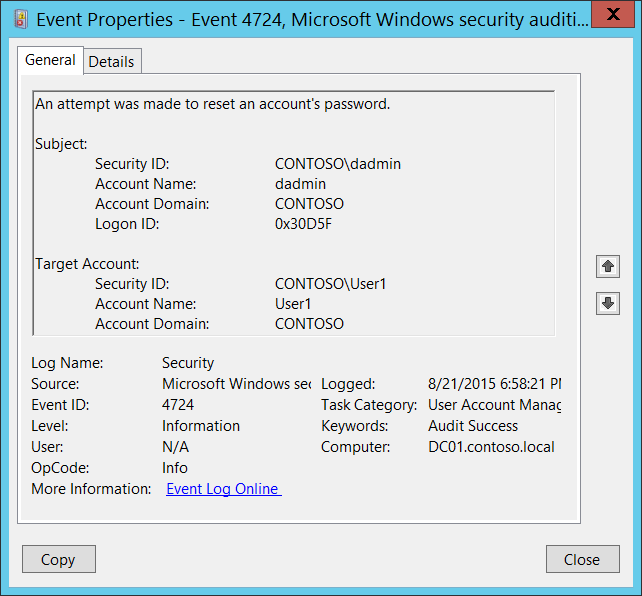 4724 S F An Attempt Was Made To Reset An Account S Password Windows 10 Windows Security Microsoft Docs
4724 S F An Attempt Was Made To Reset An Account S Password Windows 10 Windows Security Microsoft Docs
How To Filter Event Logs By Username In Windows 2008 And Higher Windows Os Hub
Komentar
Posting Komentar