Domain Trust Security Considerations
Here are some key points to keep in mind to help ensure that your trusts are. This impacts the design of security controls and may introduce vulnerabilities.
 Active Directory Security Explained 7 Best Practices Beyondtrust
Active Directory Security Explained 7 Best Practices Beyondtrust
If a group has security requirements for their own domain due to security reasons it is likely they really need their own forest he wrote.

Domain trust security considerations. An Active Directory forest may be designed with multiple domains to mitigate certain security concerns but wont actually mitigate them due to how domain trusts in the forest work. As described in Enabling Trust Between WebLogic Server Domains cross-domain security establishes trust between domains such that principals in a subject from one WebLogic domain can make calls in another domain. Trust relationships allow companies to merge domain user accounts fast and efficiently as well as have different databases for domain users even if they work for the same company.
A Trust is a legal document in which one party leaves assets to another party a trustee to be used for the benefit of a beneficiary another person charity pet etc. As stated earlier in Active Directory a forest is the only security boundary that can offer full security isolation and protection from possible security breaches. Hence I would like to understand the security risks involved in enabling 2-Way Trust.
The Ohio Secretary of States Office is responsible for overseeing elections for the state of Ohio as well as registering companies to do business in Ohio. For security considerations install Team Foundation Server in a Windows Server 2003 domain environment. One way to think about a trust is as a treasure chest.
Domain administrators of any domain in the forest have the potential to take ownership and modify any information in the Configuration container of Active Directory. WebLogic security can be enabled for each domain by adding and configuring a new Active Directory LDAP authentication provider for each. Active Directory creates a foreign security principal object in the internal domain to represent each security principal from the trusted external domain.
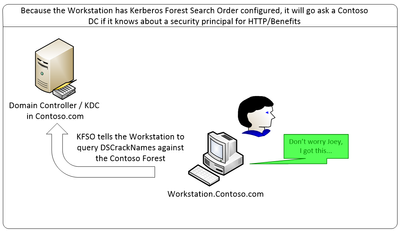
The SID history attribute is typically used by domain administrators to seamlessly migrate the user and group accounts that are held by a security principal from one domain to another. Microsoft in their KB Articles Domain Trust section Considerations About Trusts write that. This section describes important information regarding support for the cross-domain security solution.
While there are many different ways to attack Active Directory threat actors may also choose to abuse domain trust relationships. Im planning to implement 2-way Trust between these two forests for AD FS integration to provide access for users from public internet. Trusts provide flexibility for each party.
External trust 123UDP is only needed if you have manually configured the Windows Time Service to Sync with a server across the external trust. Alternatively the Domain Admin of Forest Root Domain or equivalent access through delegation can create Forest Trust. Thinking an Active Directory domain is the security boundary.
You can view the domain-wide policy by opening up the Group Policy Management Console clicking on the Default Domain Policy and navigating to Computer Configuration Windows Settings Security Settings Local Policies Security Options and looking for the policy called Domain member. In order to avoid impersonation attacks you should ban duplicate names and secure computer names by creator. The trust instrument gives specific instructions as to how to use the assets.
If Team Foundation Server is supporting work across multiple forests appropriate cross-forest trusts must be available. WebLogic Server establishes a security role for cross-domain users and uses the WebLogic Credential Mapping security provider in each domain to store the credentials to be used by. Selective authentication is a security setting that can be set on interforest trusts.
As Microsoft explains it When a trust is established between a domain in a forest and a domain outside of that forest security principals from the external domain can access resources in the internal domain. Security Considerations This model is the weakest from a security perspective. These different type of domain to domain trusts work well with Kerberos authentication although each domain must have its directory configuration set up in the GCD and the application server must have LDAP providers set up for each domain.
When security principals are created in a domain the domain SID is included in the SID of the principal to identify the domain in which it was created. Outgoing Trust Authentication Level If we want users from the specified forest to have access to all computers in the local forest on the Outgoing Trust Properties page we have to click Forest-wide authentication. Domain trusts can be complicated to administer and its important to implement changes correctly the first time.
When possible domain controllers should be configured with Trusted Platform Module TPM chips and all volumes in the domain controller servers should be protected via BitLocker Drive Encryption. This option is essential for a Windows enterprise environment so the verification of the trusts that are established is important for the audit and security perspective. According to Microsofts Security Considerations for Trusts documentation.
Gathering information about trust relationships during reconnaissance activities once an attacker has a network foothold allows them to potentially identify pathways where lateral movement would be possible. A single-forest Active Directory configuration therefore has no such secure boundaries. In datacenters physical domain controllers should be installed in dedicated secure racks or cages that are separate from the general server population.
Maximum machine account password age. Active Directory In Windows 2000 and Windows XP the Internet Control Message Protocol ICMP must be allowed through the firewall from the clients to the domain controllers so that the Active Directory.
 Practical Tips For A Cost Effective Web Hosting Web Hosting Services Hosting Company Website Hosting
Practical Tips For A Cost Effective Web Hosting Web Hosting Services Hosting Company Website Hosting
 My Paypal Account Locked Over And Over Or Is It Wealthy Relief Accounting Paypal Keep Trying
My Paypal Account Locked Over And Over Or Is It Wealthy Relief Accounting Paypal Keep Trying
 Monday Motivation Monday Motivation Cloud Computing Services Cloud Services
Monday Motivation Monday Motivation Cloud Computing Services Cloud Services
 When It Comes To Web Design There Are More Considerations That Need To Be Taken Web Design Digital Marketing Web Design Company
When It Comes To Web Design There Are More Considerations That Need To Be Taken Web Design Digital Marketing Web Design Company
 Closer Currencywhich Kickstarting A Closer Look At Those Kick Starting This New Currency Which Happens To B Cryptocurrency Financial Magazine Simple Words
Closer Currencywhich Kickstarting A Closer Look At Those Kick Starting This New Currency Which Happens To B Cryptocurrency Financial Magazine Simple Words
 10 Considerations For Your Bilingual Website By Hispanic Market Advisors Hispanicize Wire Hispanic Press Release Bilingual Hispanic Market Spanish Website
10 Considerations For Your Bilingual Website By Hispanic Market Advisors Hispanicize Wire Hispanic Press Release Bilingual Hispanic Market Spanish Website
 Pin On Security Testing Services
Pin On Security Testing Services
 Ecommerce Is A Great Way To Start Your Own Business This Infographic Highlights Some Of The Top Ben Ecommerce Startup Startup Infographic Marketing Courses
Ecommerce Is A Great Way To Start Your Own Business This Infographic Highlights Some Of The Top Ben Ecommerce Startup Startup Infographic Marketing Courses
 How To Centralize Dns Management In A Multi Account Environment Amazon Web Services Dns Accounting Domain Name Service
How To Centralize Dns Management In A Multi Account Environment Amazon Web Services Dns Accounting Domain Name Service
 The Resistance Of Using Cloud Models Has Faded Due To The Fact That Sophisticated Cloud Security Software Has Been Proven Reliable Another Security Google Drive
The Resistance Of Using Cloud Models Has Faded Due To The Fact That Sophisticated Cloud Security Software Has Been Proven Reliable Another Security Google Drive
A Guide To Attacking Domain Trusts Harmj0y
 Report Compliance With Regulatory Policies And In House Security Policies Home Security Regulatory Policies
Report Compliance With Regulatory Policies And In House Security Policies Home Security Regulatory Policies
 Lepide Active Directory Self Service Software Tool This Or That Questions Active Directory Database Management System
Lepide Active Directory Self Service Software Tool This Or That Questions Active Directory Database Management System
 Best Bluehost Discounts In 2016 Https S3 Amazonaws Com Bluehost Coupon Codes Index Html Virtual Private Server Server Room Web Hosting
Best Bluehost Discounts In 2016 Https S3 Amazonaws Com Bluehost Coupon Codes Index Html Virtual Private Server Server Room Web Hosting
 Create An Ad Ds Resource Forest In Azure Azure Reference Architectures Microsoft Docs
Create An Ad Ds Resource Forest In Azure Azure Reference Architectures Microsoft Docs
 Angular And Owasp Top 10 Security Cheat Sheet 2020 Practical Advice Web Security Cyber Security
Angular And Owasp Top 10 Security Cheat Sheet 2020 Practical Advice Web Security Cyber Security
 Rental Lease Agreement Rental Agreement Forms Ez Landlord Forms Lease Agreement Being A Landlord Room Rental Agreement
Rental Lease Agreement Rental Agreement Forms Ez Landlord Forms Lease Agreement Being A Landlord Room Rental Agreement

Komentar
Posting Komentar